Foreword
Health Care and Public Health Sector Cybersecurity Framework Implementation Guide
Today's climate of increasingly sophisticated cyberattacks exploit fragmented hospital infrastructures, an often-unwieldy number of applications and legacy, and network-connected medical devices, which can negatively impact patient care, cripple business operations, expose sensitive health data, and negatively impact a company's reputation and market value. Additionally, lack of attention to regulatory compliance increases the risk of delivery of care, in addition to fines and other penalties. These risks drive corporate boards and executive management teams to adapt to the ever-changing threat landscape and improve their overall approach to cyber governance and security.
Many, if not most, health care organizations struggle with managing cybersecurity effectively. The Office for Civil Rights (OCR) HIPAA Audits Industry Report found that 86% of Covered Entities (CEs) and 83% of Business Associates (BAs) (85% collectively) did not meet expectations for a Risk Assessment. For Risk Management, 94% of CEs and 88% of BAs (91% collectively) did not meet expectations.[2] In 2019, as reported, OCR continued to find the failure to conduct an accurate and thorough risk analysis as one of the most frequent violations of the HIPAA Security Rule by organizations that OCR has entered into resolution agreements with, or that have been found to have violated HIPAA.[3],[4] While compliance is an important factor in securing the information technology environment, undertaking a broader collaborative engagement in a risk analysis will enhance the ability to effectively identify and manage organizational risk, safeguard patient privacy, and protect business value.
Federal agencies with regulatory oversight for health care organizations have the ability to hold health care organizations responsible for implementing reasonable and appropriate cybersecurity practices. And, in addition to data centric cyber concerns, health care organizations should be cognizant of Cyber Physical Systems (CPS) and Internet of Things (IoT) security issues[5] that can adversely impact health care operations and patient care.[6]
To be effective in today’s constantly evolving threat and regulatory compliance landscape, health care organizations must adopt an approach that goes beyond the threats, vulnerabilities and controls
du jour and helps communicate how cybersecurity investments result in meaningful risk reduction. Senior leadership has a crucial strategic role to play in developing and managing such an approach, but they are often hampered by their limited understanding of cyber issues, the quality and frequency of the reporting they receive from management, and inadequate governance structures.
One way organizations can improve their ability to manage cyber-related risk is to adopt a comprehensive cybersecurity framework that can provide a common language and structure for discussions around risk and the methods and tools used to manage risk to a level that is not only acceptable to the organization but to other stakeholders such as business partners, customers, and industry and governmental regulators. Basing an organization’s cybersecurity program on an industry-recognized cybersecurity framework can also help direct capital, operational, and resource allocations to lines of business generating the greatest return on protecting assets/information and minimizing risk exposure.
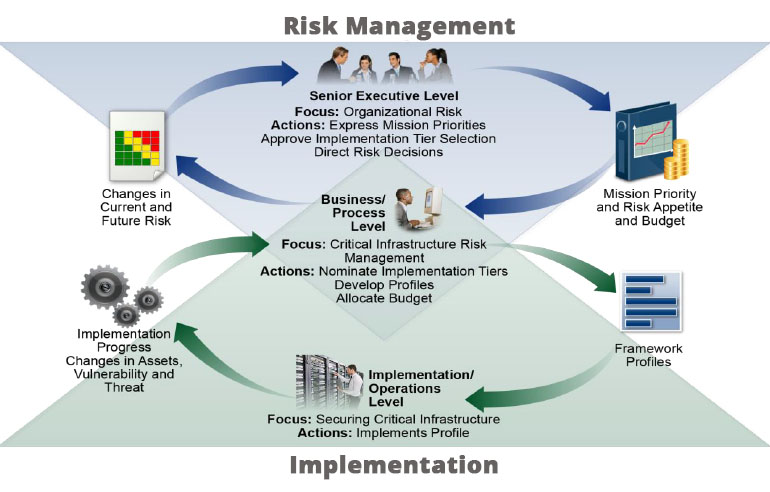
Figure 1. Notional Information and Decision Flows within an Organization[7]
The “Health Industry Cybersecurity Practices: Managing Threats and Protecting Patients” publication (HICP),[8] recognizes the complexity of cybersecurity threats. This publication, which was developed by the joint public-private 405(d) Task Group, covers the five most prevalent threats in the HPH Sector and 10 cybersecurity practices to help mitigate these threats. Within its Technical Volumes, the cybersecurity practices and sub-practices are mapped to the National Institute of Standards and Technology (NIST) Cybersecurity Framework. Additionally, the Task Group developed a HICP Threat Mitigation Matrix that includes the NIST Cybersecurity Framework and HIPAA Security Rule crosswalk. HHS concurred with the recommendation of the 405(d) Task Group in the report and stated that it would work with appropriate entities to assist in sector adoption.
One of the frameworks recommended by the Task Group to help health care organizations manage cybersecurity and bolster their security posture is the NIST Framework for Improving Critical Infrastructure Cybersecurity (“Cybersecurity Framework”). This document, the
HPH Sector Cybersecurity Framework Implementation Guide, is intended to help HPH Sector organizations implement the NIST Cybersecurity Framework as an integral part of their cybersecurity and cyber risk management programs.
Leveraging the NIST Cybersecurity Framework also aligns with the National Association of Corporate Directors (NACD) Director’s Handbook on Cyber-Risk Oversight,[9] which provides five key issues that corporate boards should consider as they oversee cybersecurity and cyber risk management programs:
- Approach cybersecurity as an enterprise-wide risk management issue, not just an IT issue.[10]
- Understand the legal implications of cyber risk as they apply to the company’s specific circumstances.
- Ensure they have adequate access to cybersecurity expertise, and discussions about cyber-risk management should be given regular and adequate time on the board meeting agenda.
- Set the expectation that management will establish an enterprise-wide cyber-risk management framework.
- Include identification of which risks to either avoid, accept, mitigate, or transfer through insurance, as well as specific plans associated with each approach, in discussions of cyber risks between the Board and organizational management.
Organizations need a practical approach for addressing cybersecurity challenges. Boards and executive management want better insight into how cybersecurity management decisions are made. The NIST Cybersecurity Framework bridges the communications divide between an organization’s leadership and the information technology and security teams, helps define cyber maturity targets, supports complex cyber risk management decisions, and improves Board oversight of cybersecurity and cyber risk management programs.
<< Back Next >>
2 OCR (2020, Dec).
2016-2017 HIPAA Audits Industry Report.
3 OCR (2019, Feb)
OCR Concludes 2018 with All-Time Record Year for HIPAA Enforcement.
4 For more information on settled enforcement actions, see OCR (2022).
Resolution Agreements: Resolution Agreements and Civil Money Penalties.
5 National Institute of Standards and Technology, NIST(2021).
Cyber-Physical Systems (CPS) and Internet of Things (IoT).
6 Parker, S. (2017, Oct 3.).
Understanding the Physical Damage of Cybersecurity. In Information Security Magazine.
7 NIST (2018, Aug 16).
Framework for Improving Critical Infrastructure Cybersecurity, Version 1.1. Wash., DC: Author, p. 12.
8 HHS (2022a).
Health Industry Cybersecurity Practices: Managing Threats and Protecting Patients.
9 Clinton, L. (Ed.) (2020).
Cyber-Risk Oversight (Director’s Handbook Series). Arlington, VA: National Association of Corporate Directors.
10 For more information on how to integrate cybersecurity into enterprise risk management, see Stine, K., Quinn, Stephen, Witte, G., and Gardner, R. (2020, Oct).
Integrating Cybersecurity and Enterprise Risk Management (ERM) (NISTIR 8286). Gaithersburg, MD: NIST, p. 2.

